Online Digital Forensics Courses and Labs
Building a Low-cost and State-of-the-art IoT Security Hands-on Laboratory
Funded by National Science Foundation (NSF)
Funded by Cyber Florida

IoT Firmware Analysis
Computer Setup:
- Download VMWare Player from here and install it.
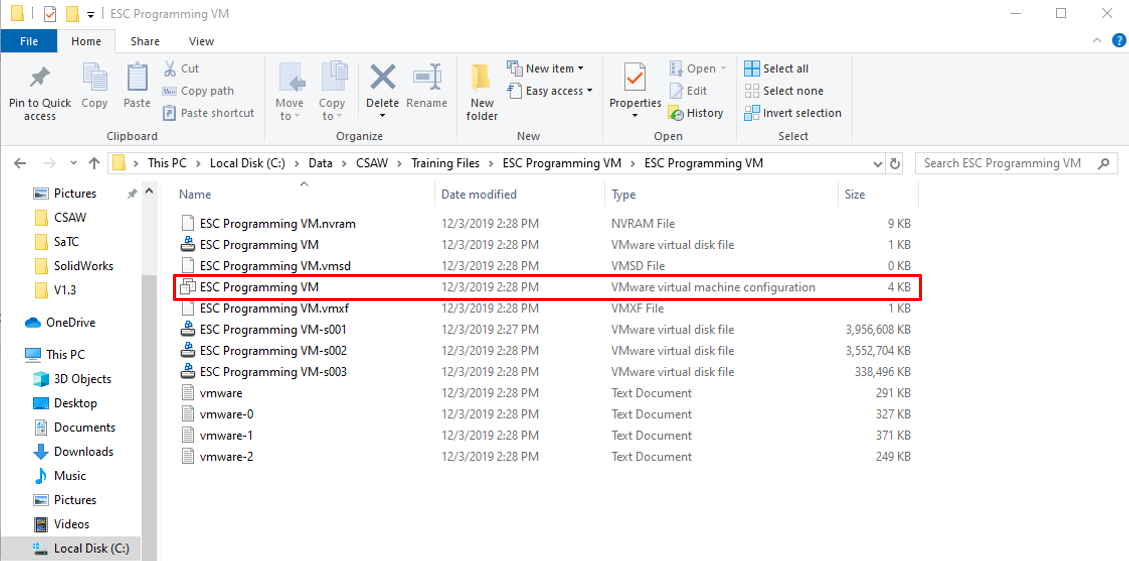
- Download the Linux VM from here and unzip the folder to desired location.
- Open the following application.
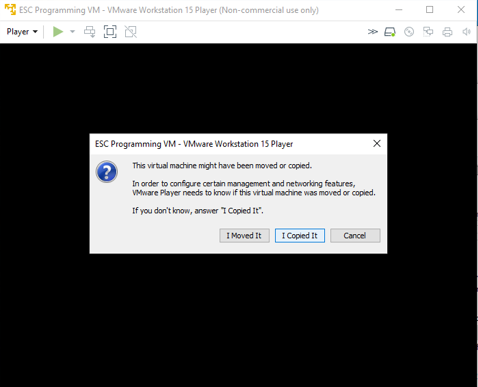
- Once the VM is opened it asks if the machine was moved or copied. Select "I Copied It". Do not perform any updates to the machine.
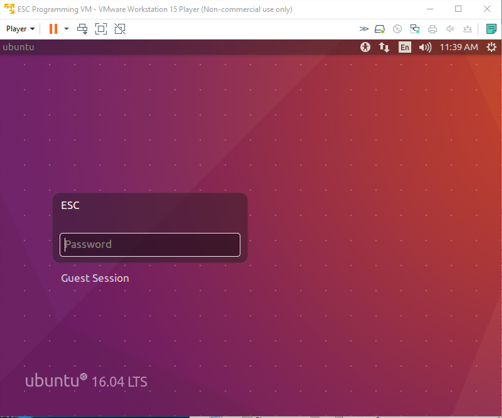
- Log in to the ESC account using password: esc
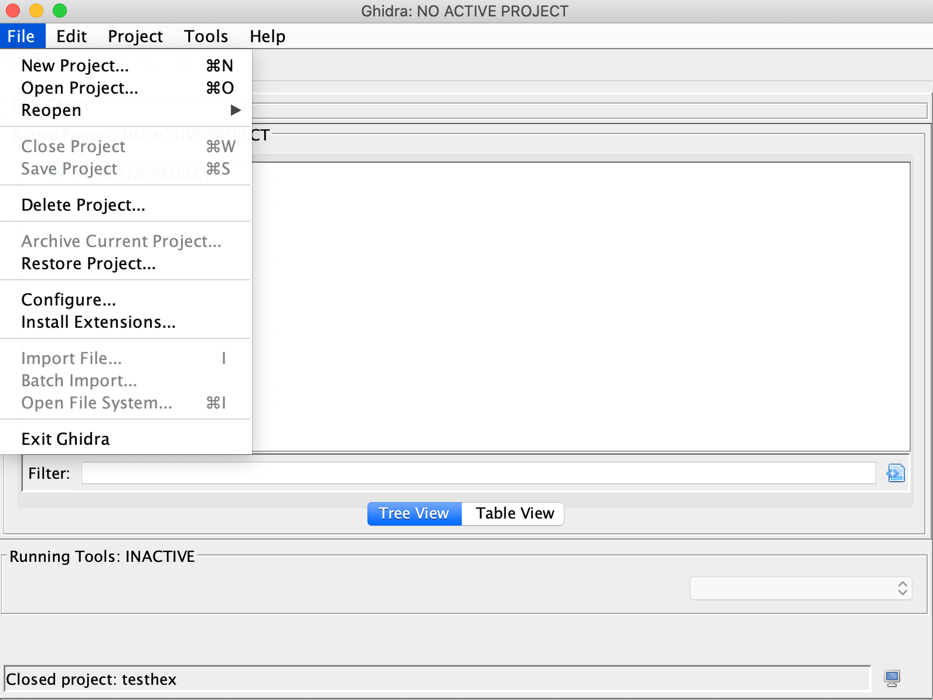
- Download Ghidra for Linux from here or from its website https://ghidra-sre.org/ and install it. The installation guide can be found under the docs folder. Note that the Java environment is required to be set up, and the guide can also be found in the installation guide.
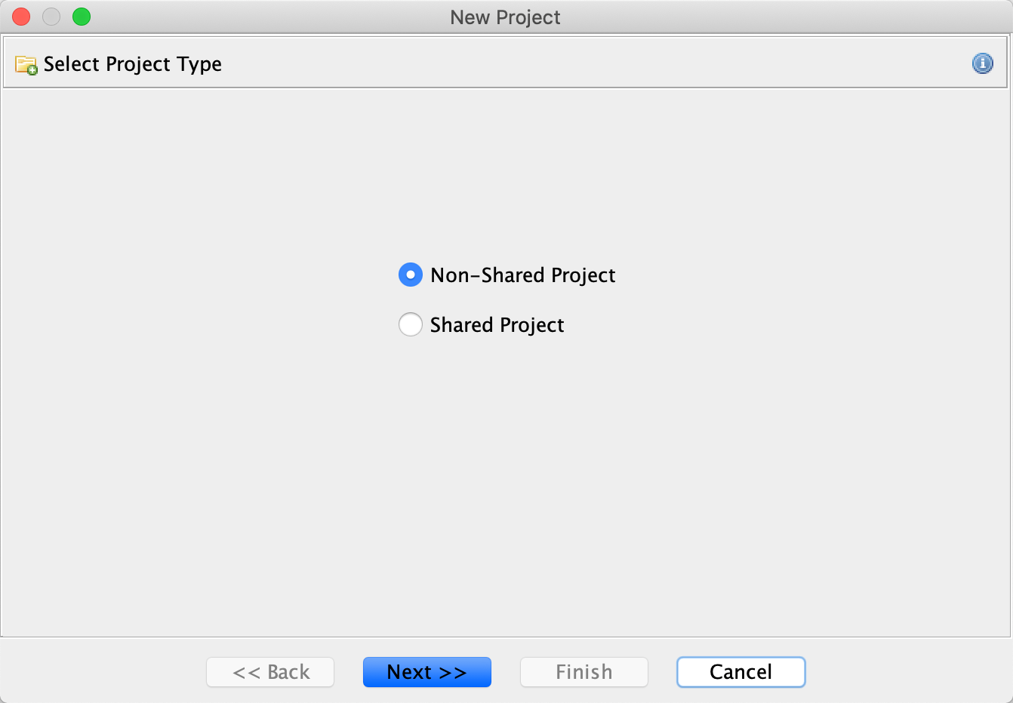
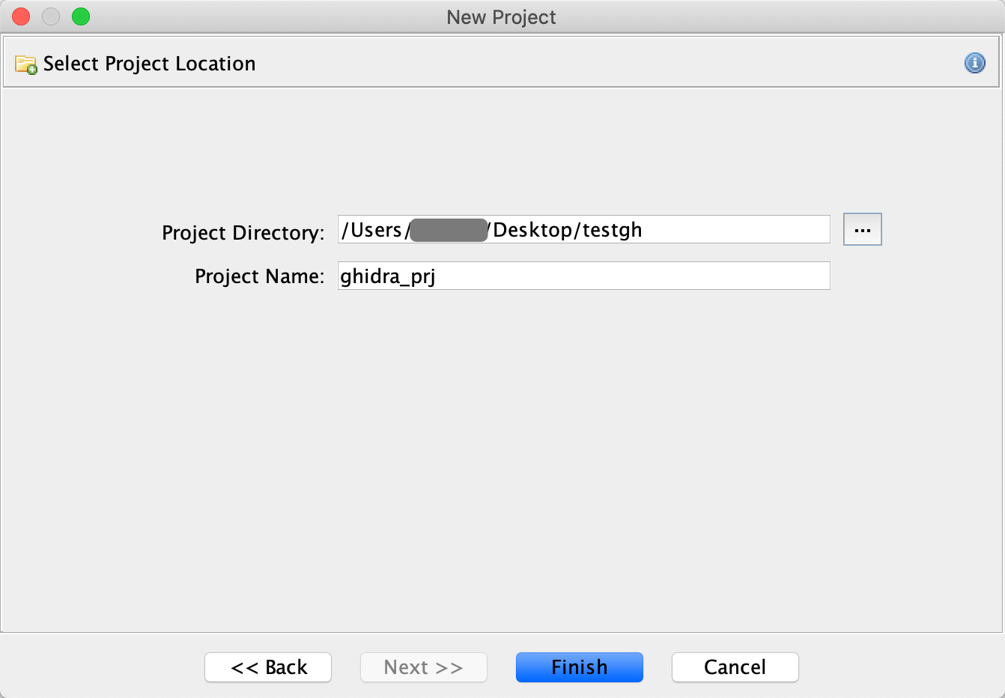
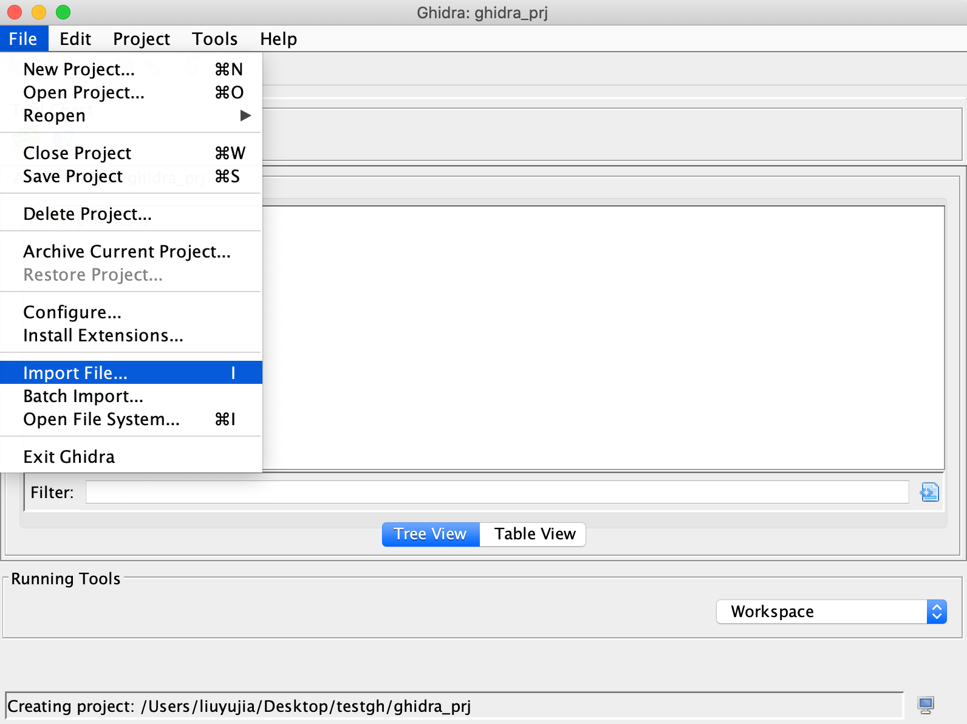
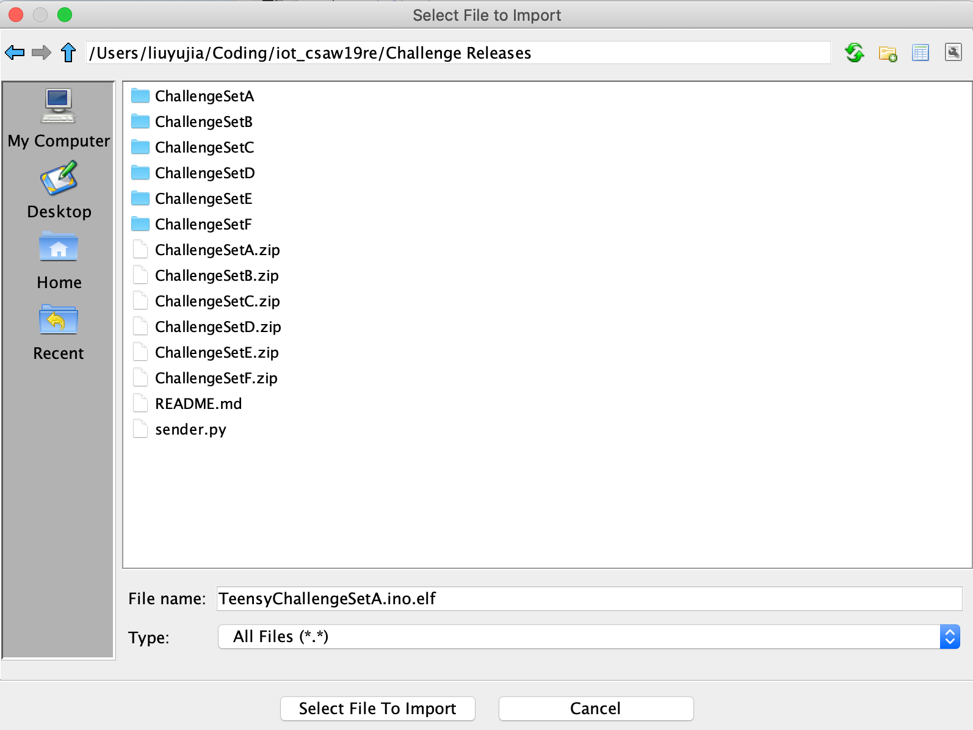
Experimentation Setup:
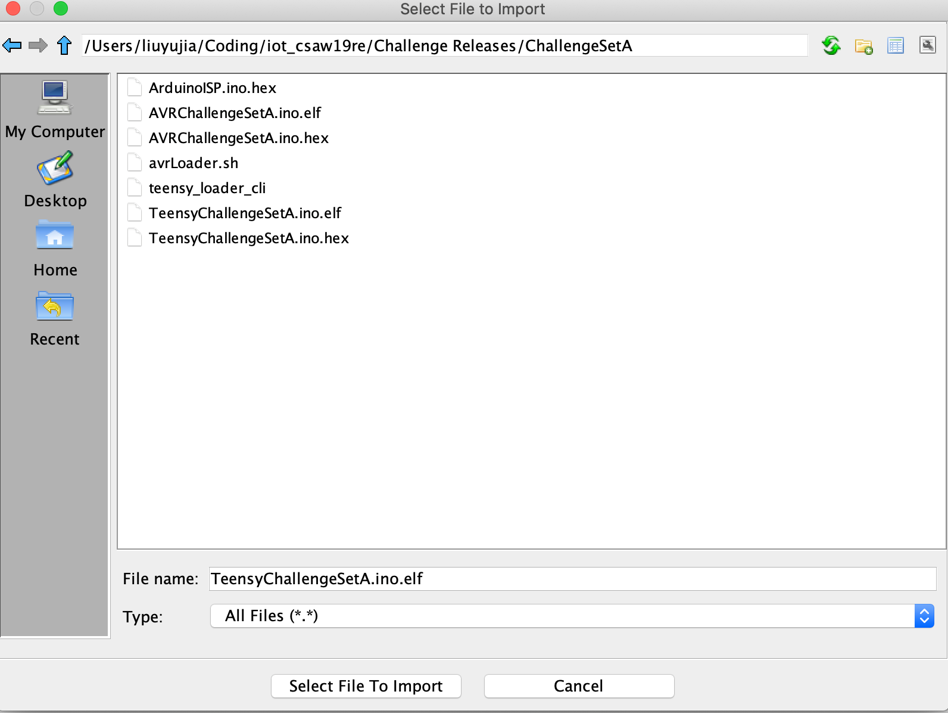
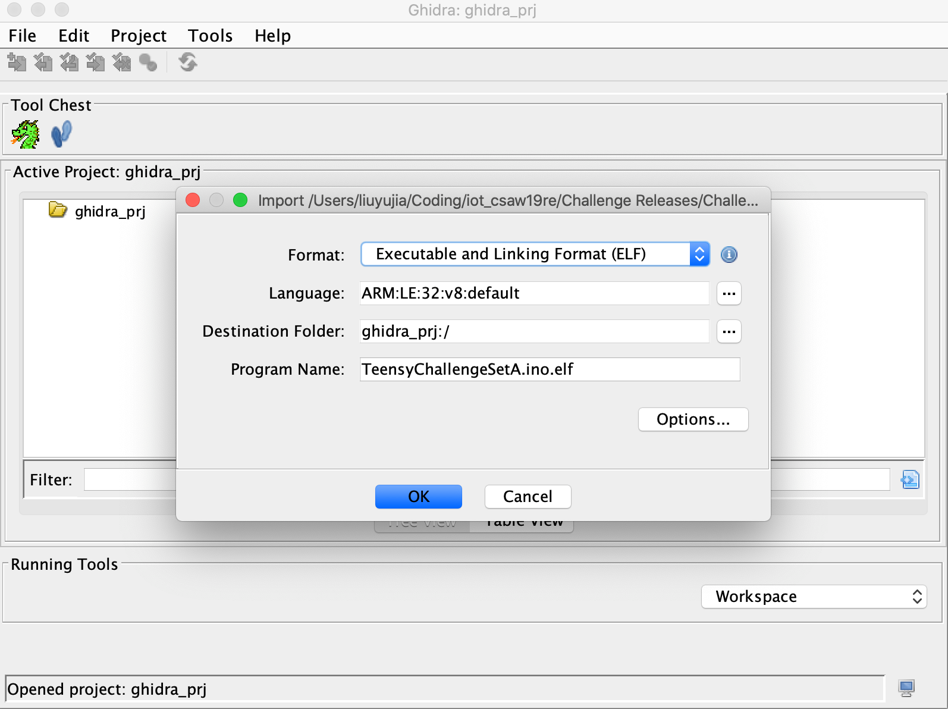
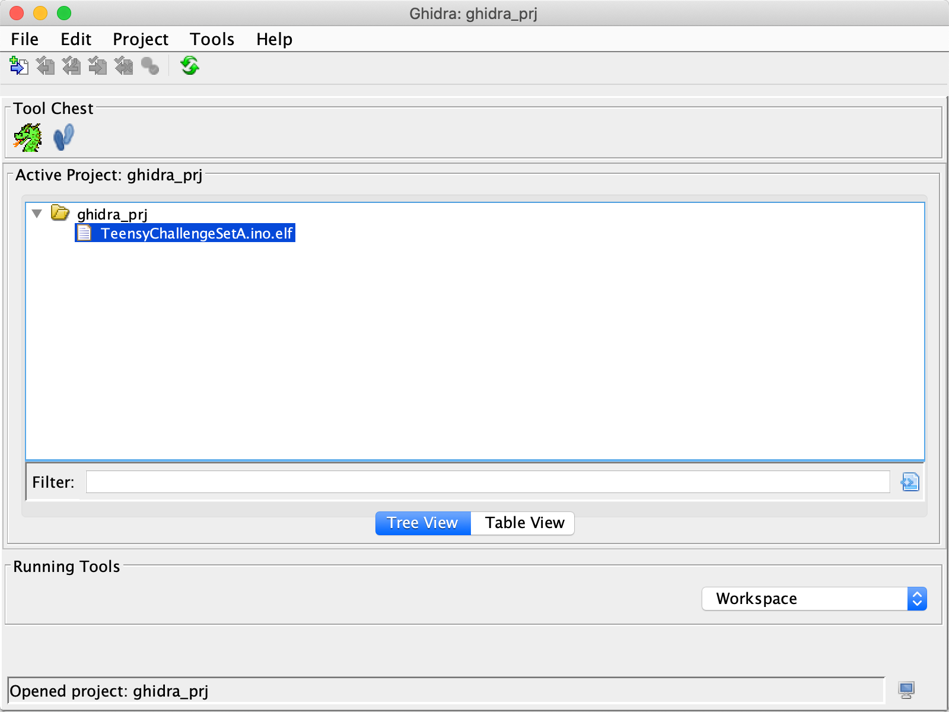
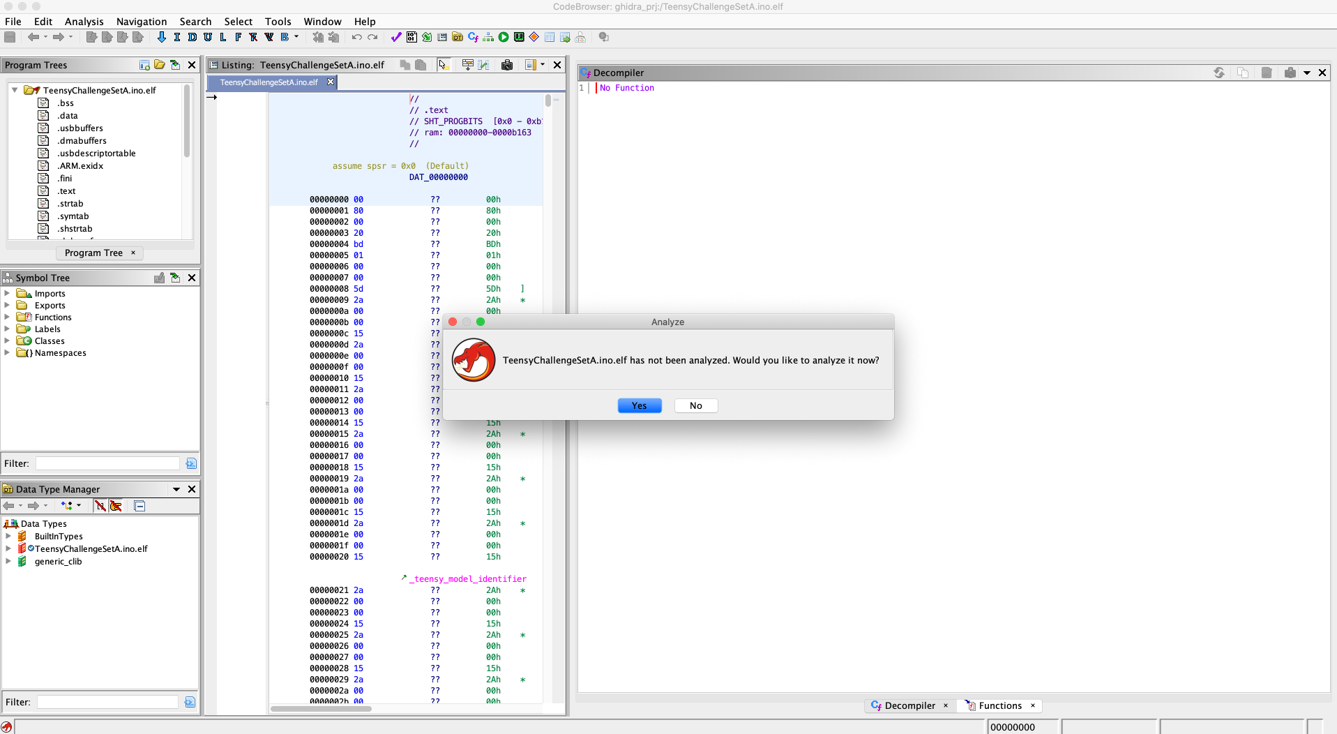
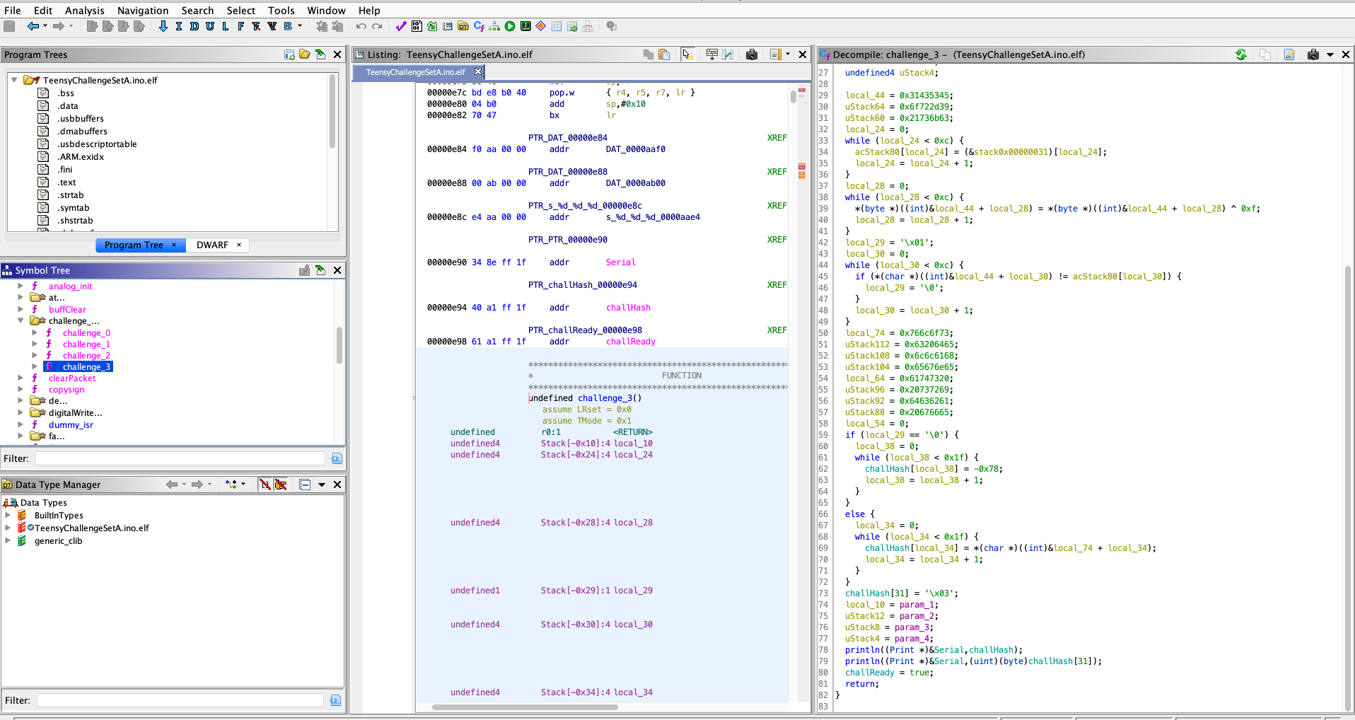
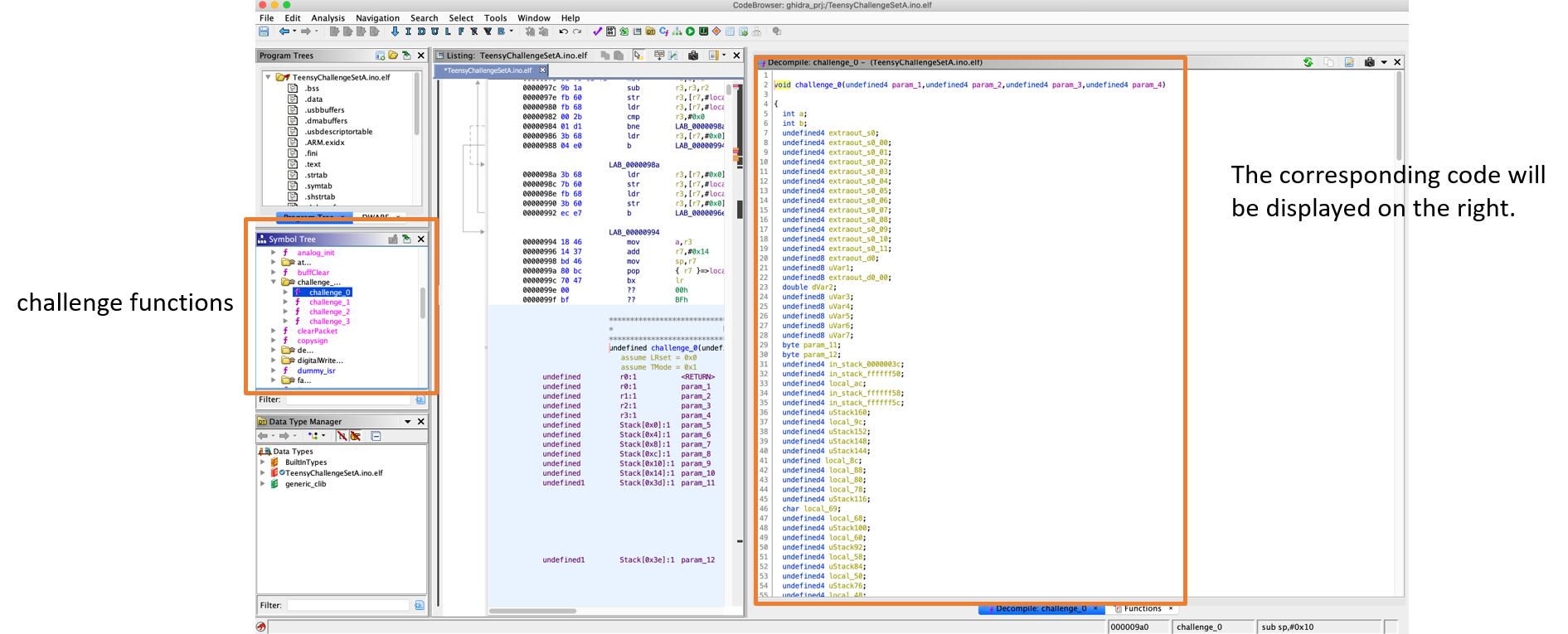
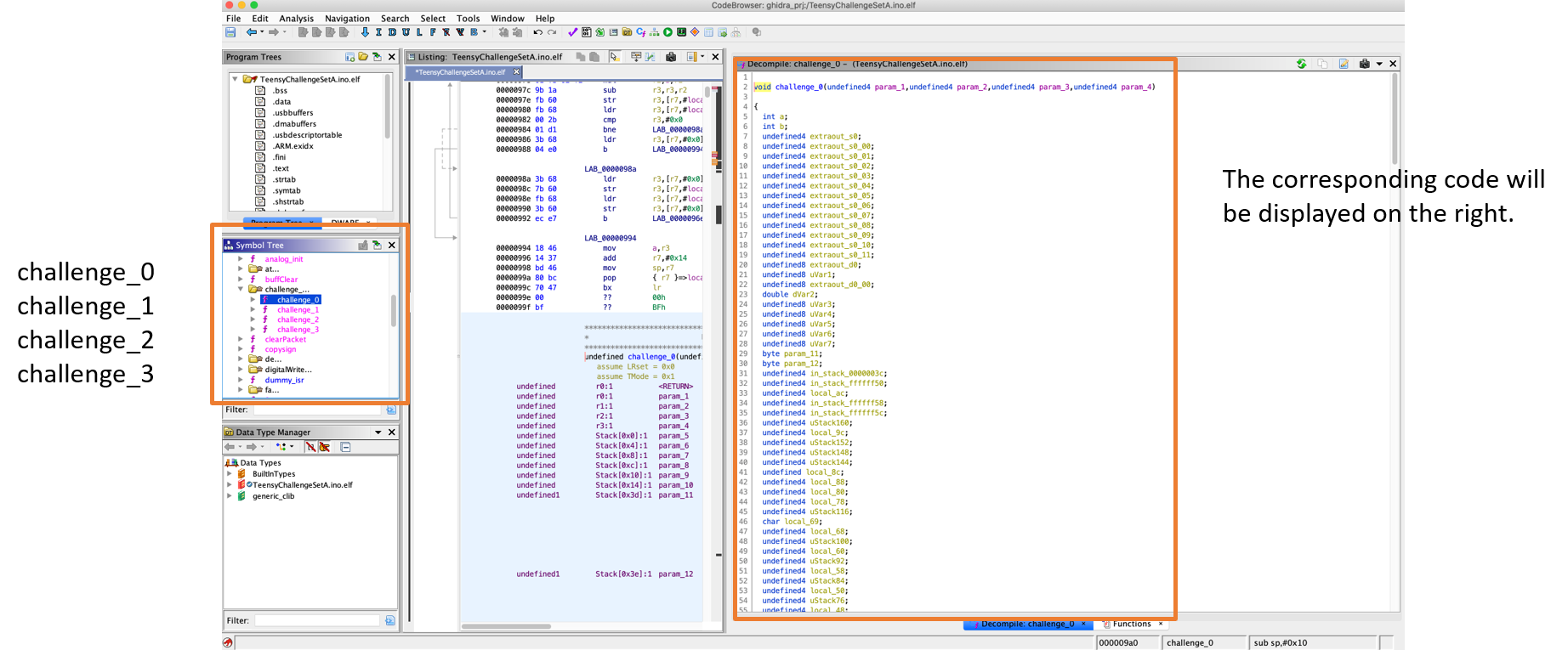
- Use Ghidra to inspect the binary.
- Useful Tools: Symbol Tree
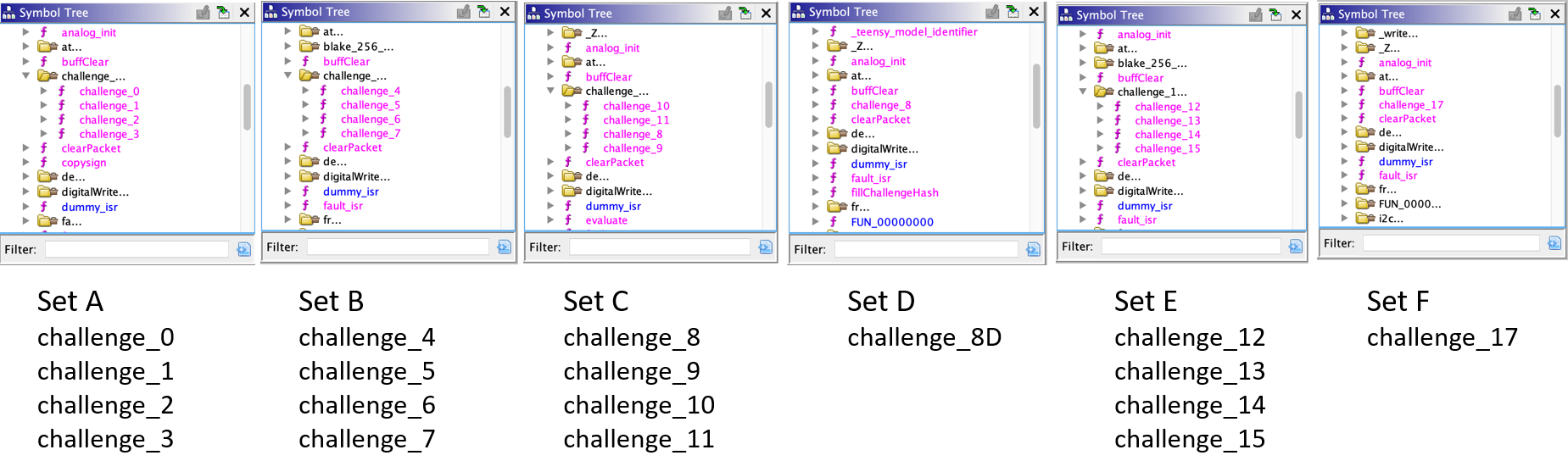
- Repeat in other folders, all the challenge functions are located.
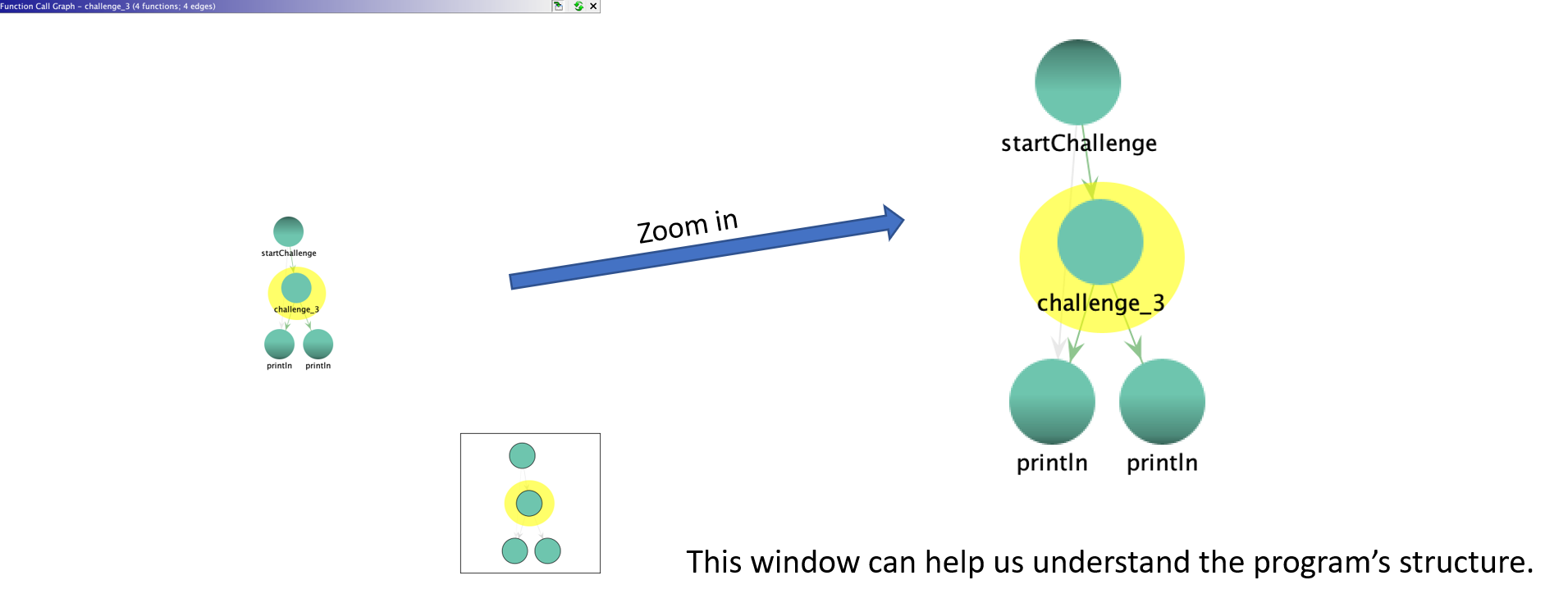
- Useful Tools: Window -> Function Call Graph
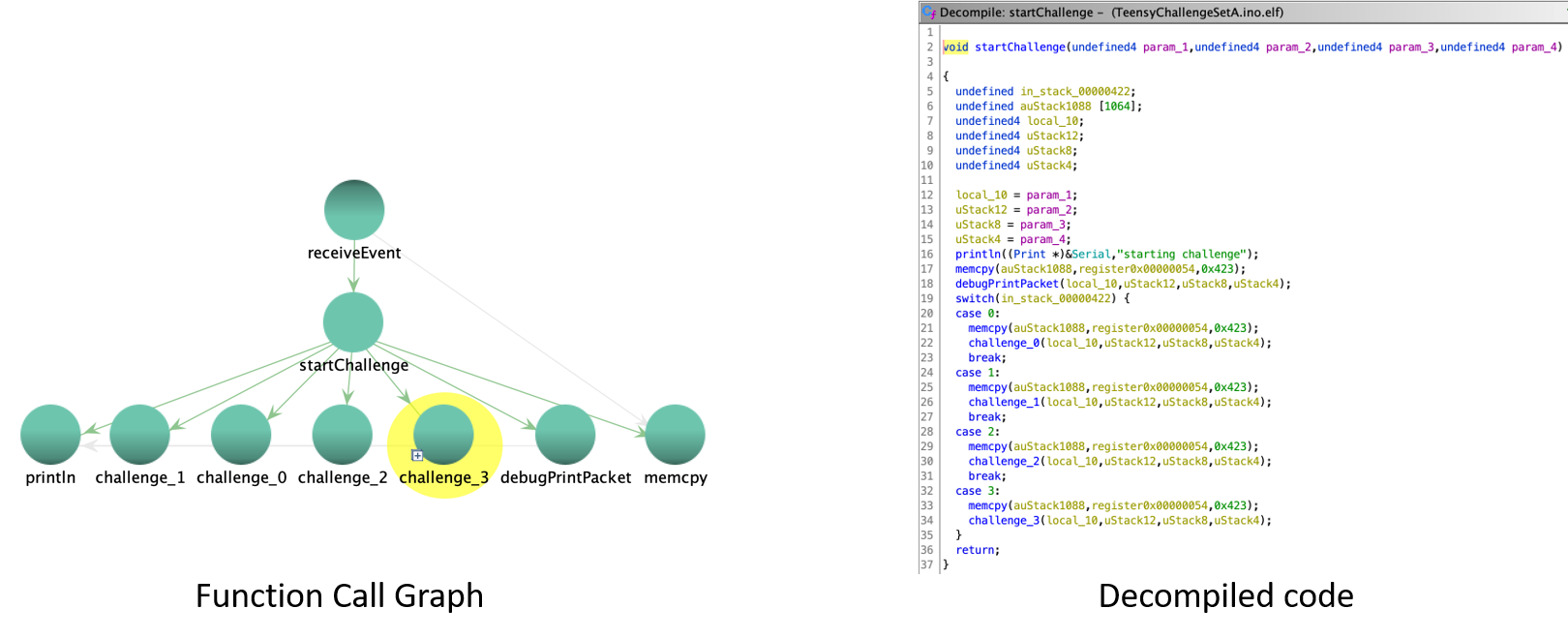
- Double click "startChallenge". Now we can see details in Decompile window.
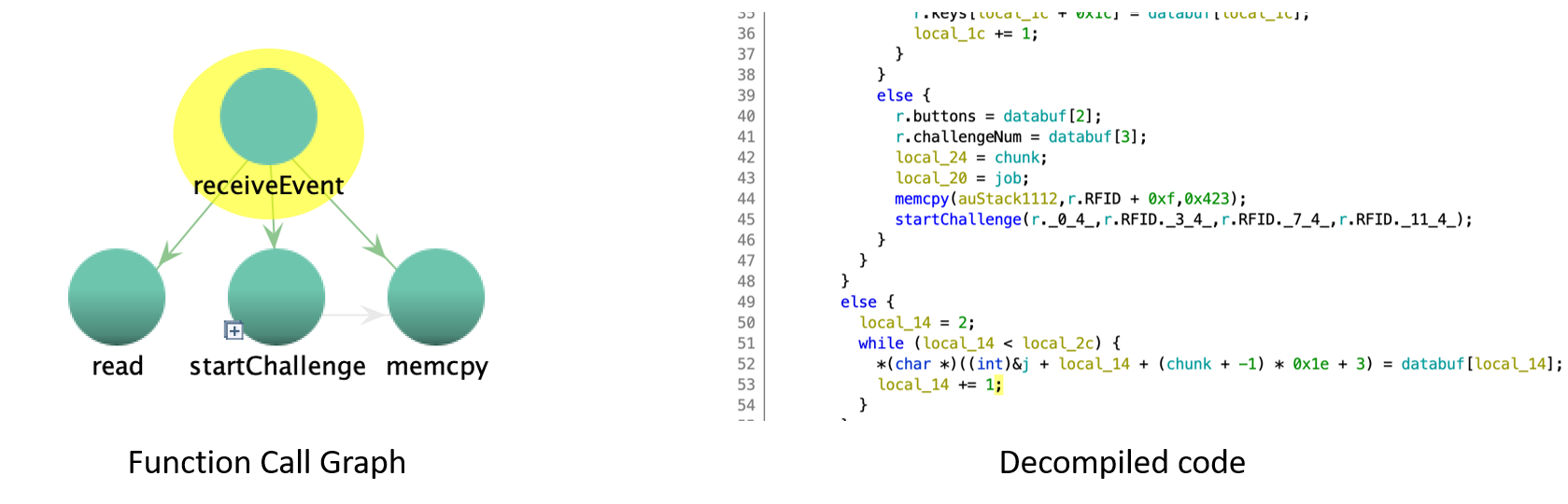
- It is clear that the whole program is Event-Driven. Locate the challenges input.
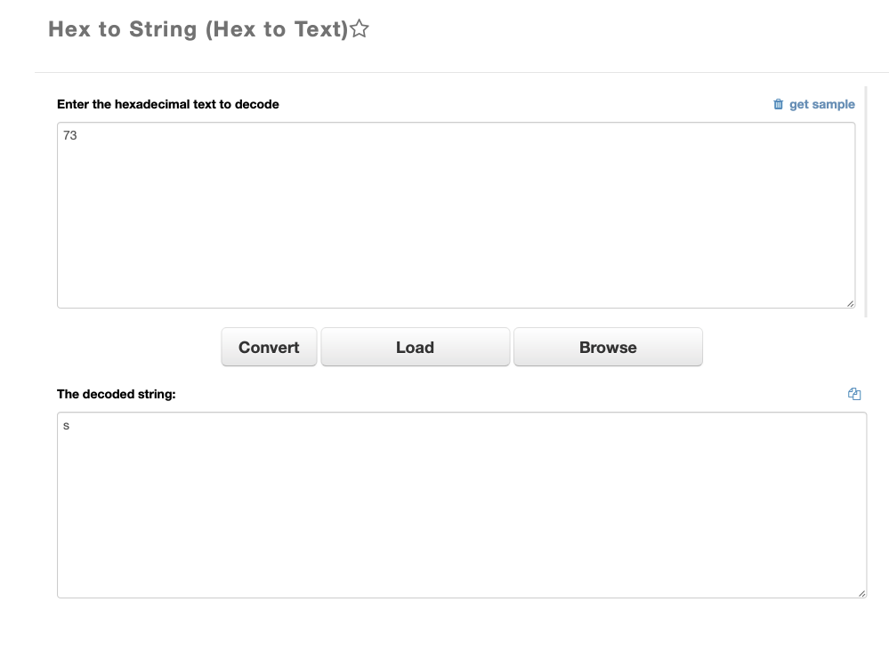
- Useful Tools: Hex to String Convertor.
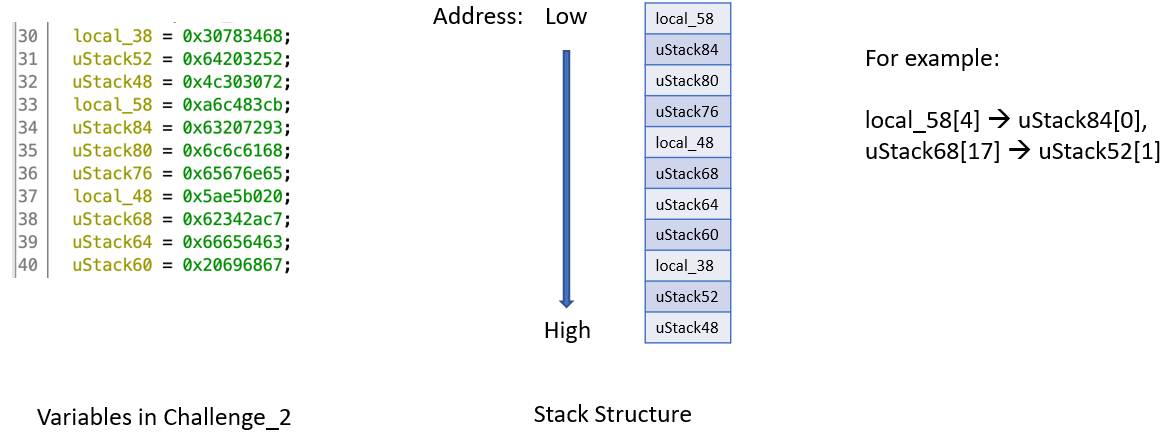
- A little instruction about naming rules in Ghidra.
Warmup Example: Stairs
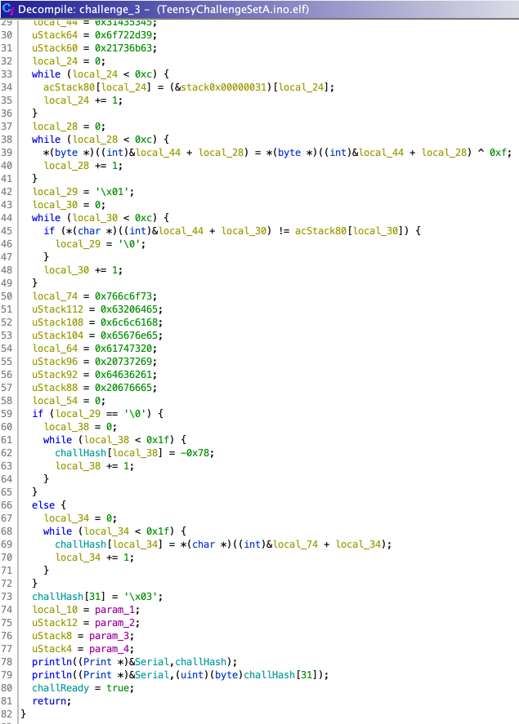
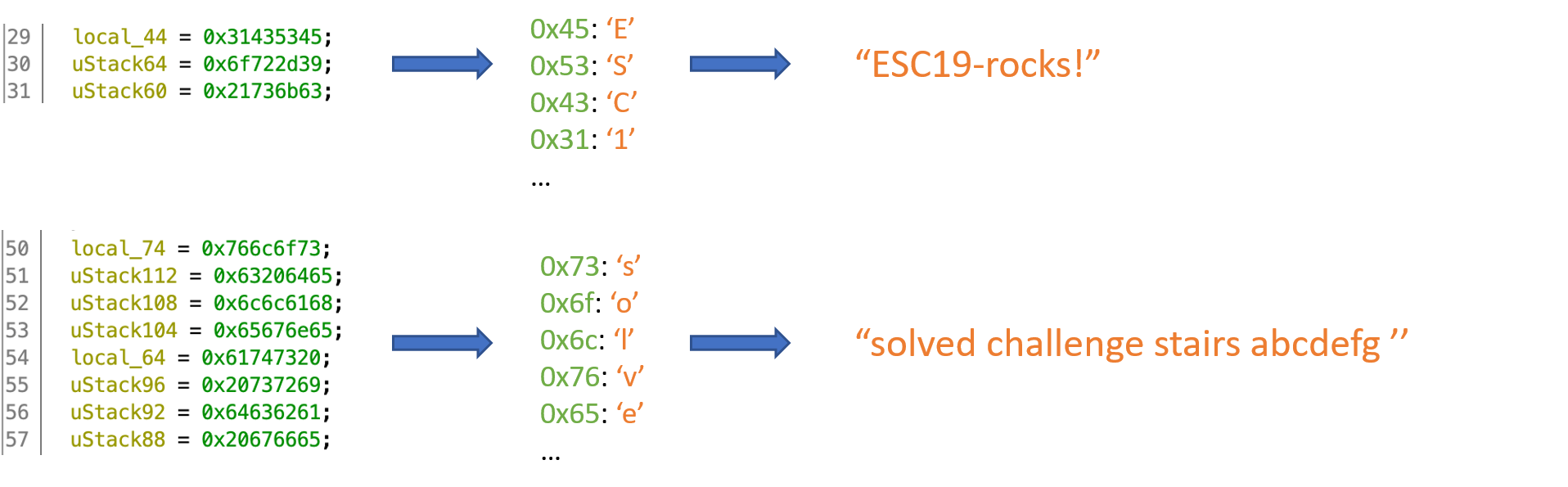
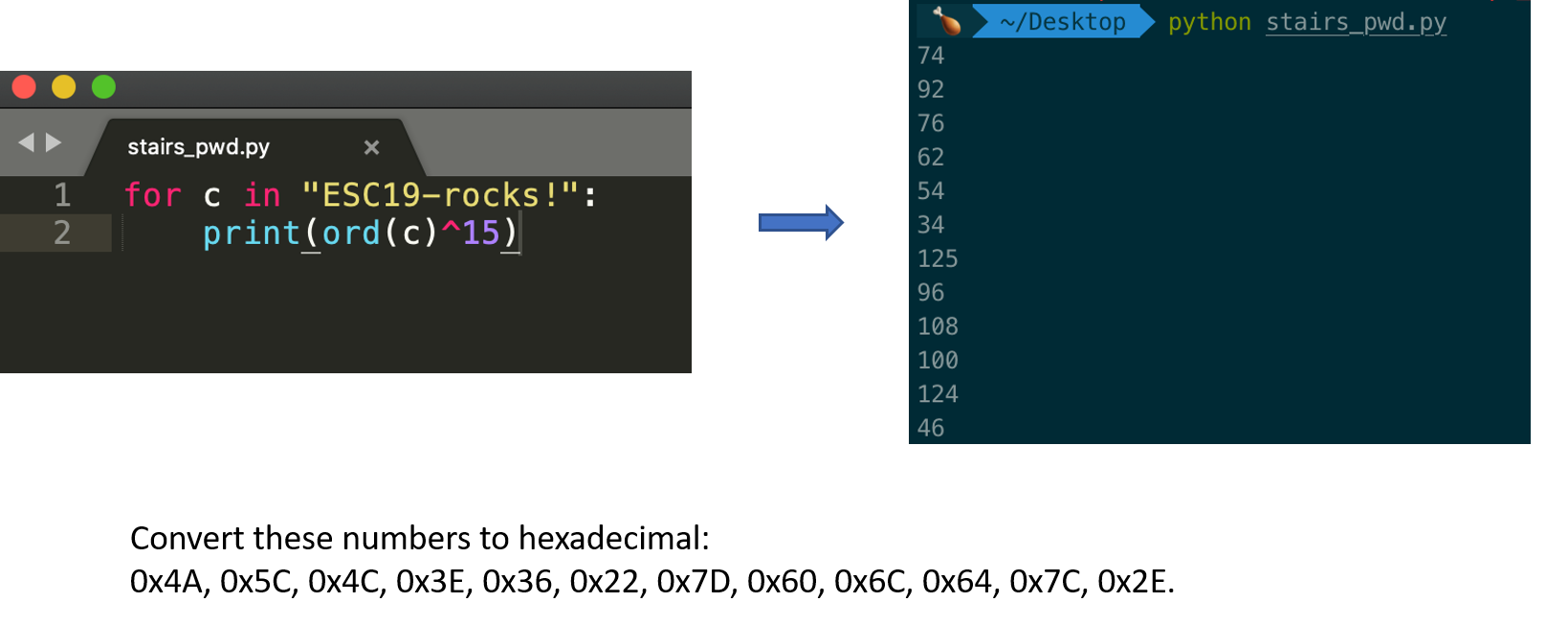
- In the following, we will give an example with challenge_3 Stairs. The Stairs challenge is using 12 bytes of the RFID (from byte 64 to byte 75). Each character in the string "ESC19-rocks!" is XORed by 15 and this is the value we need to provide using the RFID. The source code is as follows:
- Clue #1: Using a reverse engineering tool to inspect the binary, we can see that the string "ESC19-rocks!" is being used.
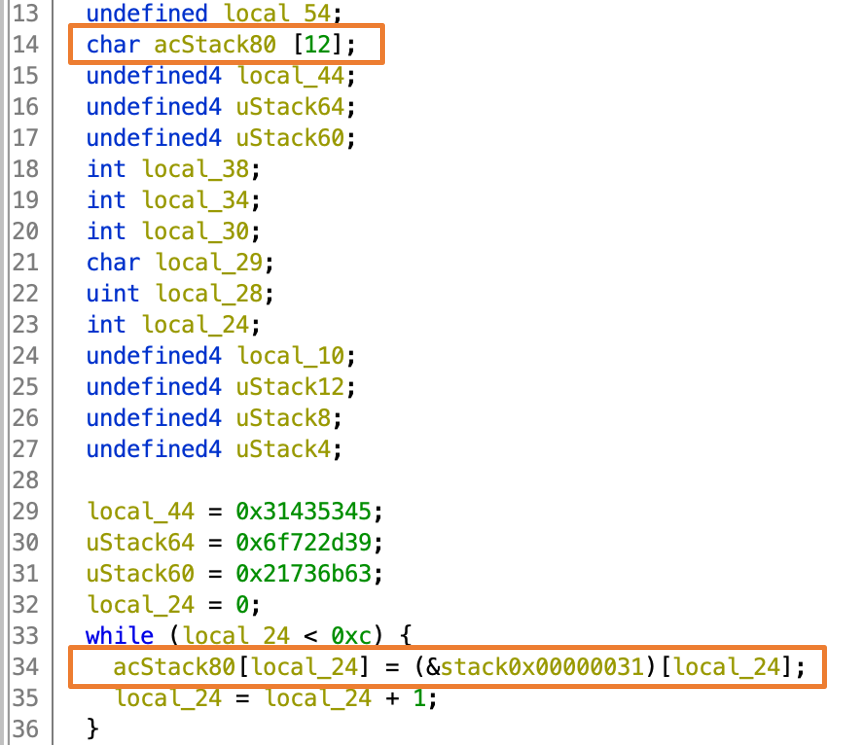
- Clue #2: We observe that a loop initializes an array using values from the RFID starting at offset 64. Here is what the source code looks like:
- Clue #3: We also observe that each character of the initial string is XORed with 15. Here is what the source code looks like:
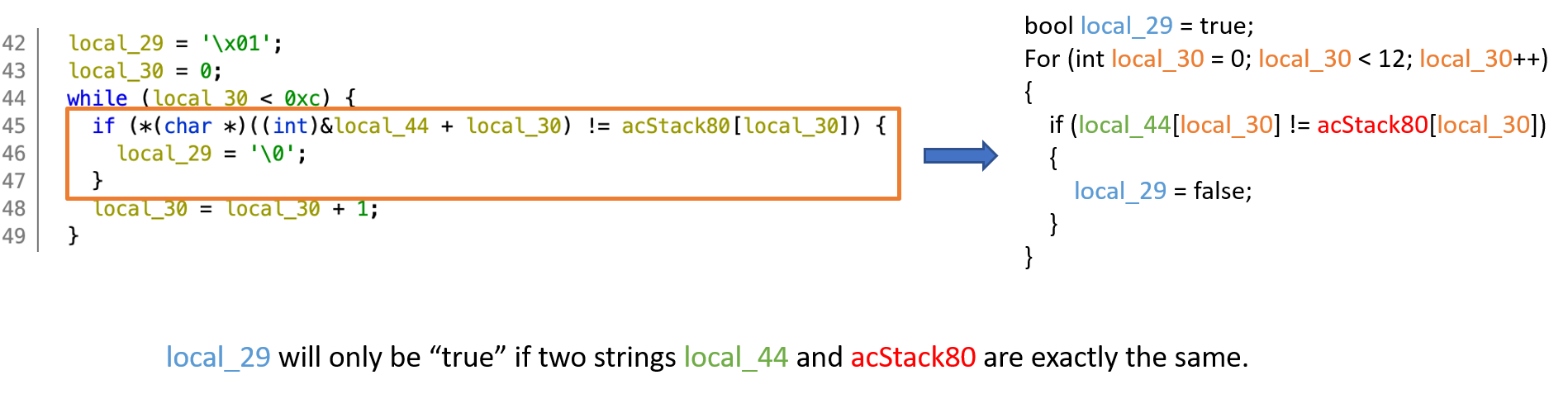
- Clue #4: Finally, the XORed string and the provided string are compared. Here is what the corresponding source code looks like:
- To identify what values we should put in the pwd array, we have to XOR each character of the "ESC19-rocks!" string with 15. This can be done in Python:
- We are almost there! We now know which bytes to use, but we need to figure out where to put them in the RFID...
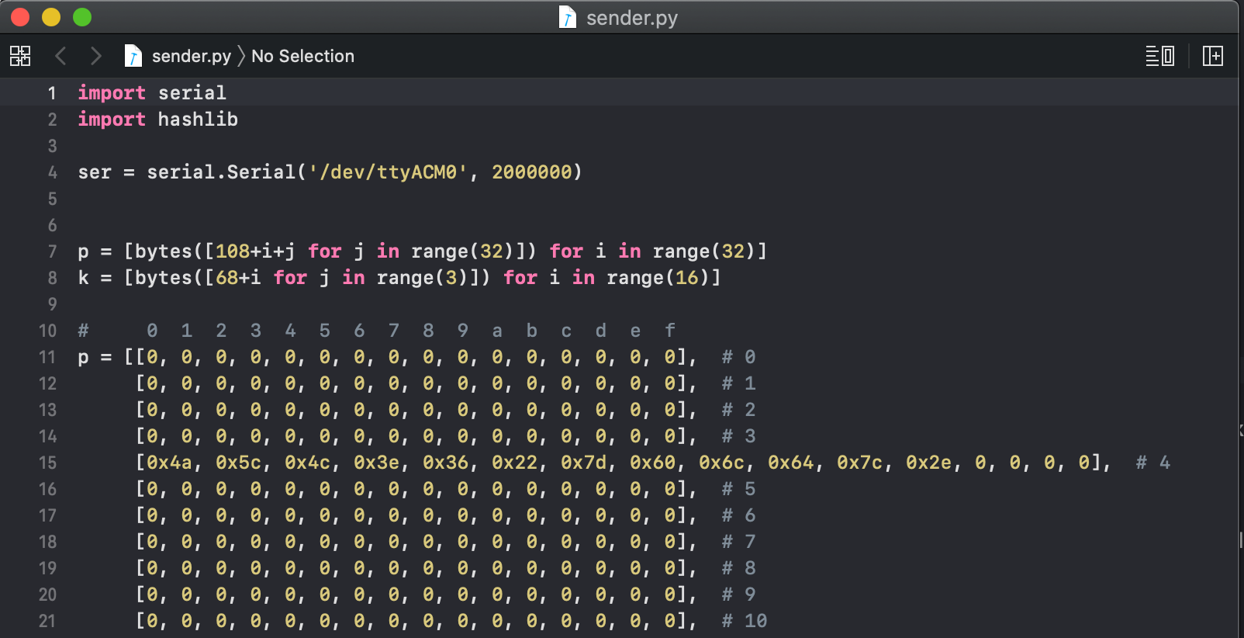
- Clue #5: Since the array is initialized using a statement like pwd[i] = r.RFID[64 + i], this means that for i = 0 the 64th RFID byte is read and placed at index 0. In the next iteration the 65th byte is placed at pwd[1], and so on.
- Thus, sender.py should have ord('E')^15 in the 64th position and so on.
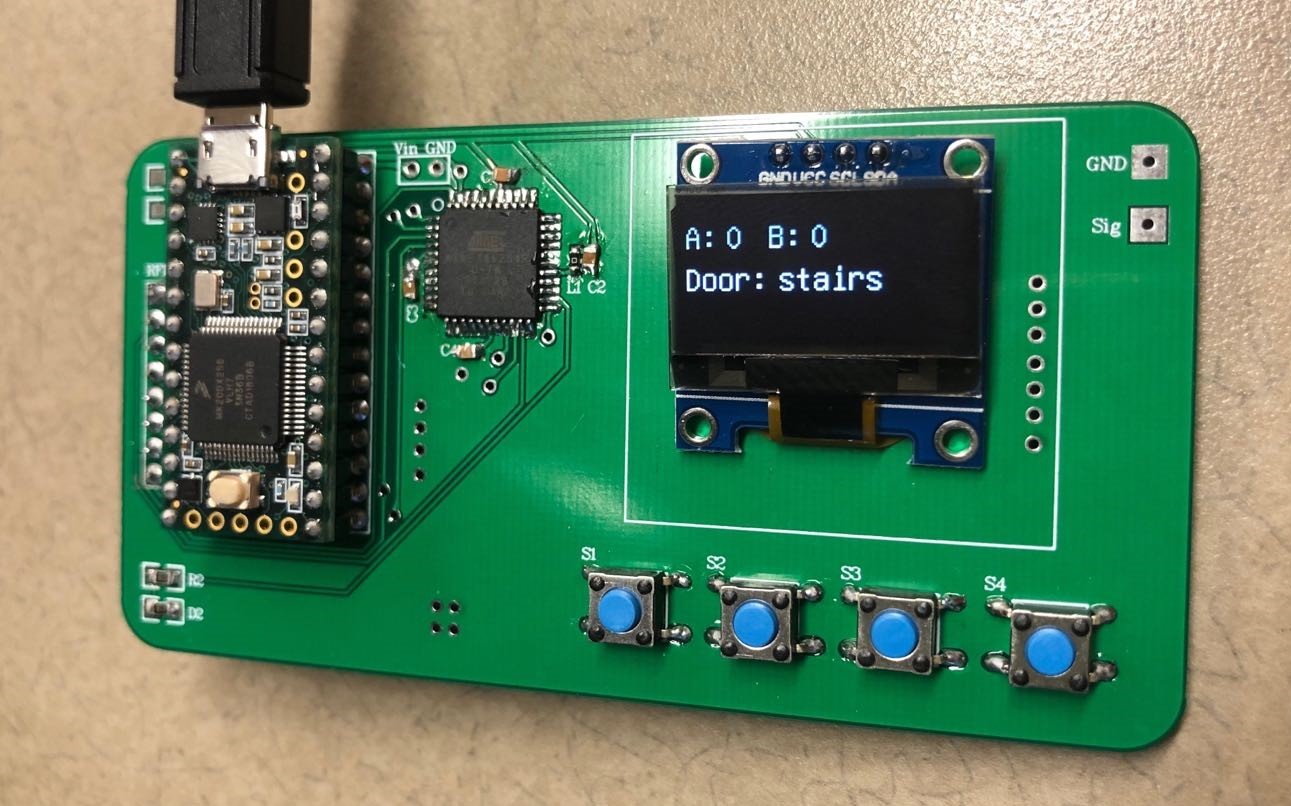
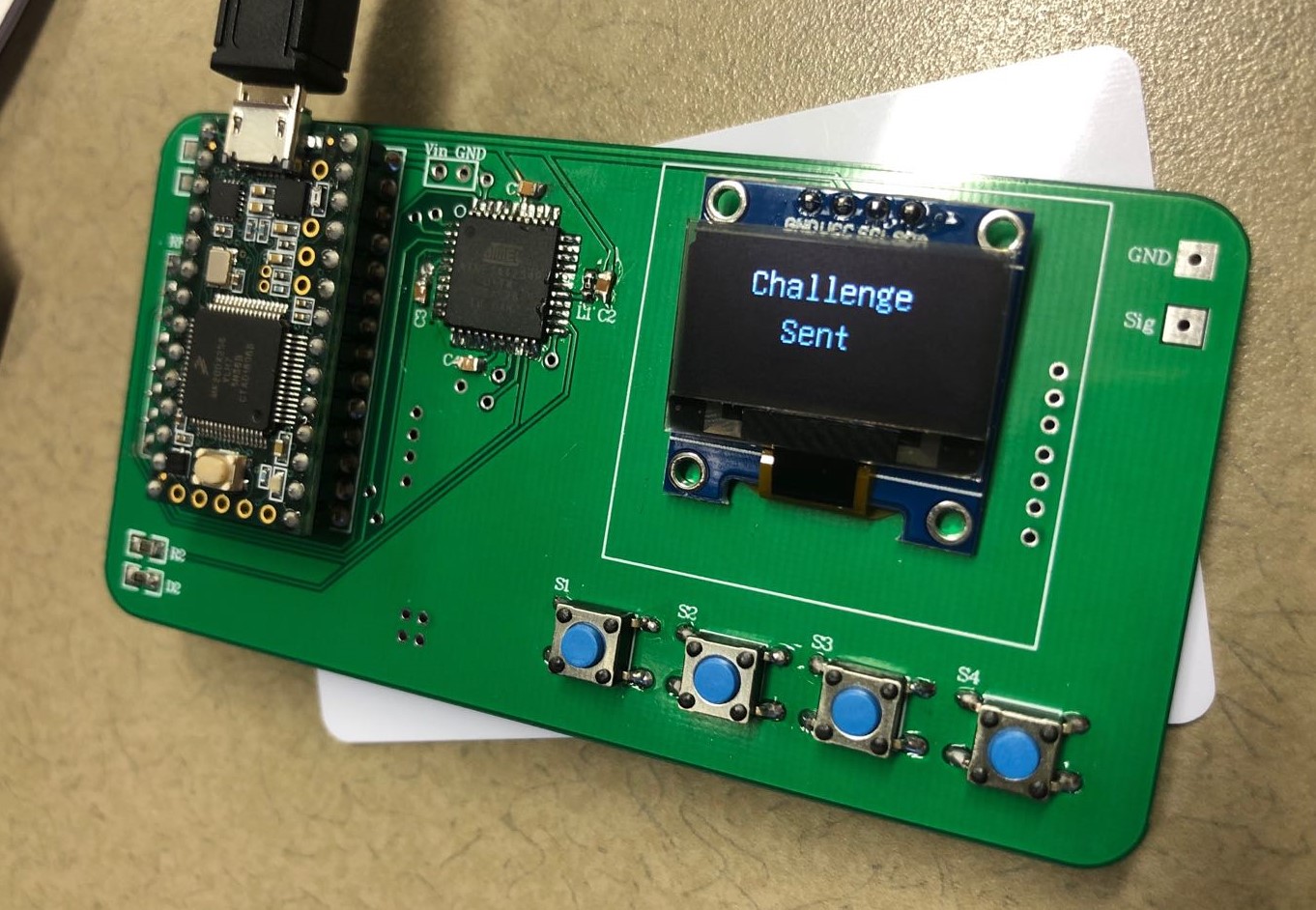
- Push button S1 to find the challenge we are working on.
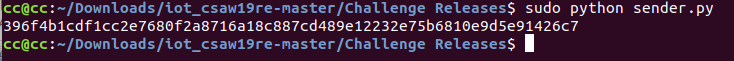
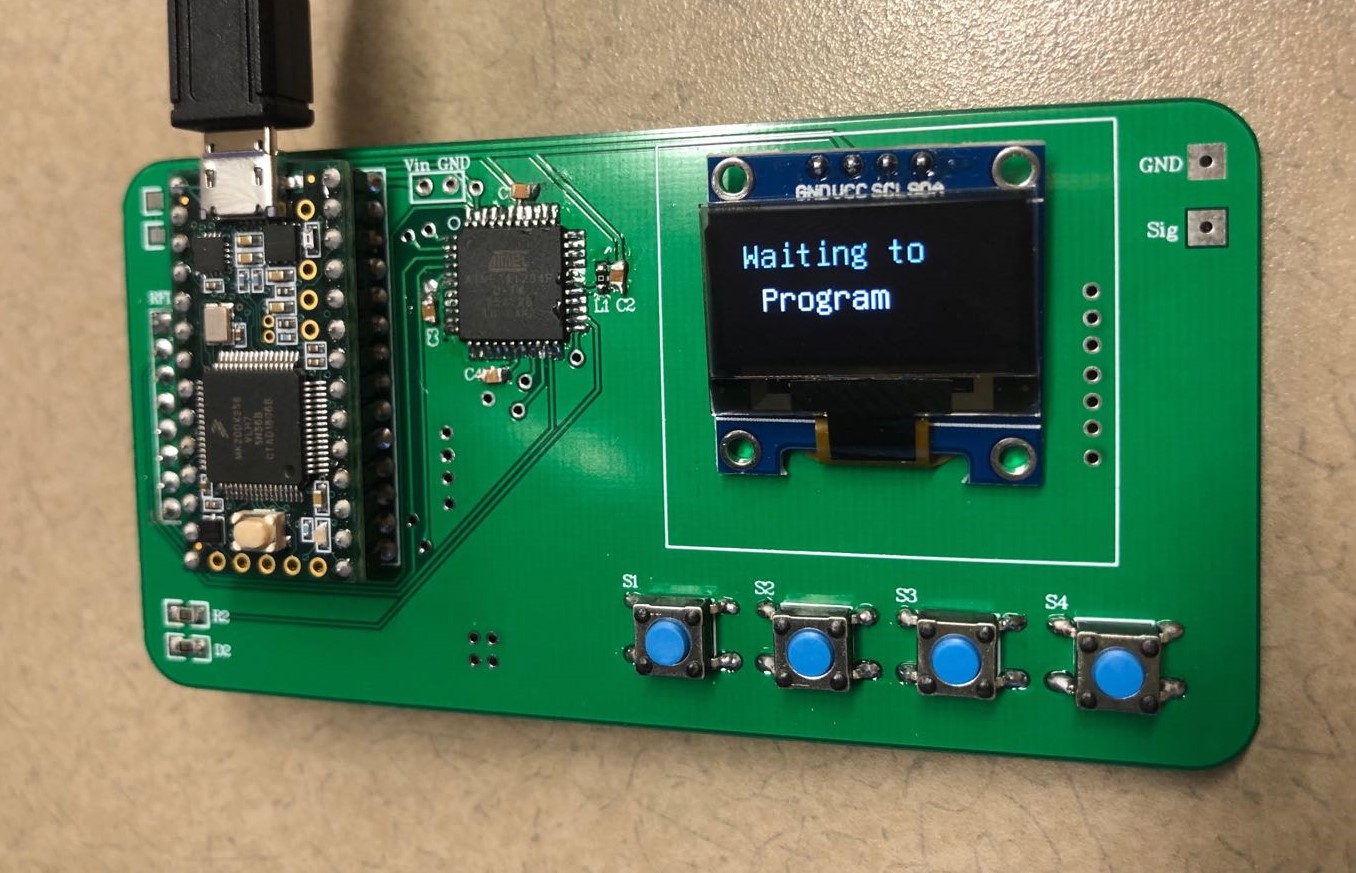
- Connect the board to your computer, and run sender.py. The bytes will be written to the board automatically.
- Put the RFID card close to the board, then the data will be written to the card.
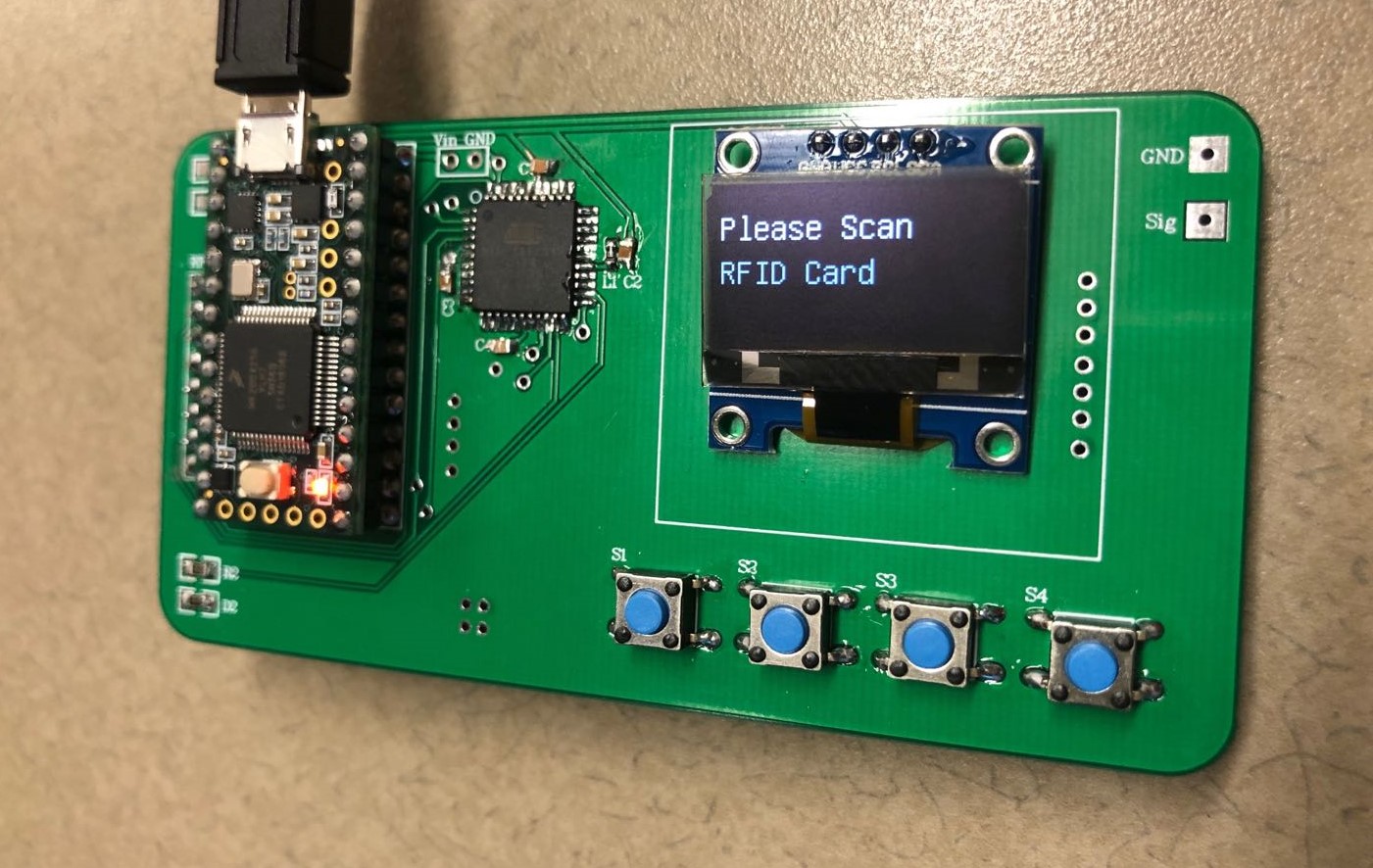
- Push button S4 to read the RFID card.
- Put the RFID card close to the board, then the data will be read.
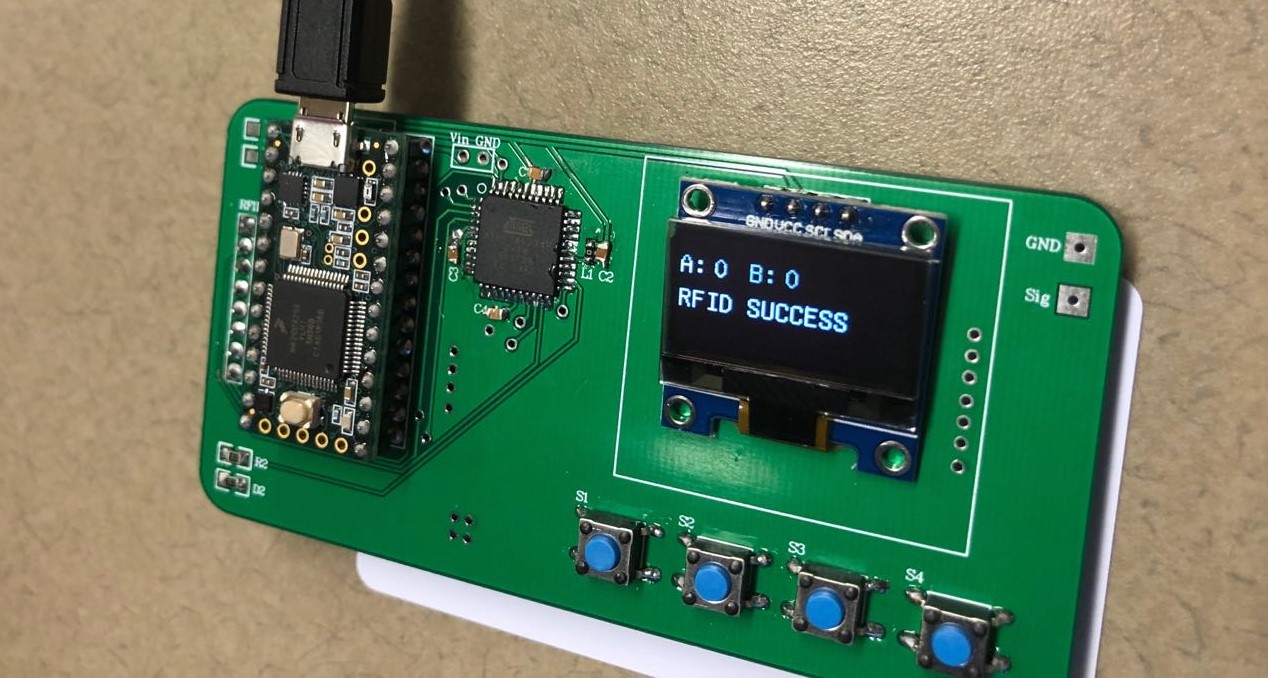
- You will see from the LCD whether the answer is correct.